TheDeveloperBlog.com
C-Sharp | Java | Python | Swift | GO | WPF | Ruby | Scala | F# | JavaScript | SQL | PHP | Angular | HTML
DBMS Lock based Protocol
DBMS Lock based Protocol with DBMS Overview, DBMS vs Files System, DBMS Architecture, Three schema Architecture, DBMS Language, DBMS Keys, DBMS Generalization, DBMS Specialization, Relational Model concept, SQL Introduction, Advantage of SQL, DBMS Normalization, Functional Dependency, DBMS Schedule, Concurrency Control etc.
Lock-Based ProtocolIn this type of protocol, any transaction cannot read or write data until it acquires an appropriate lock on it. There are two types of lock: 1. Shared lock:
2. Exclusive lock:
There are four types of lock protocols available:
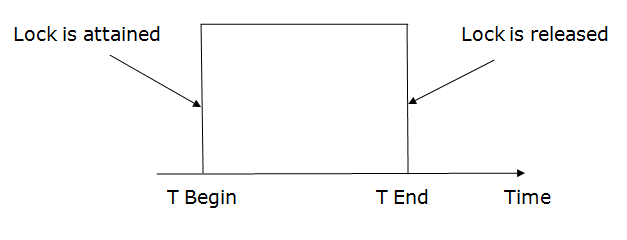
1. Simplistic lock protocolIt is the simplest way of locking the data while transaction. Simplistic lock-based protocols allow all the transactions to get the lock on the data before insert or delete or update on it. It will unlock the data item after completing the transaction. 2. Pre-claiming Lock Protocol
3. Two-phase locking (2PL)
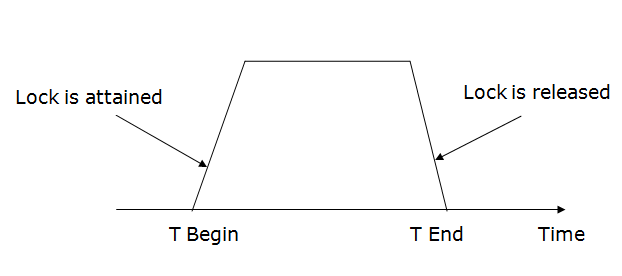
There are two phases of 2PL: Growing phase: In the growing phase, a new lock on the data item may be acquired by the transaction, but none can be released. Shrinking phase: In the shrinking phase, existing lock held by the transaction may be released, but no new locks can be acquired. In the below example, if lock conversion is allowed then the following phase can happen:
Example: 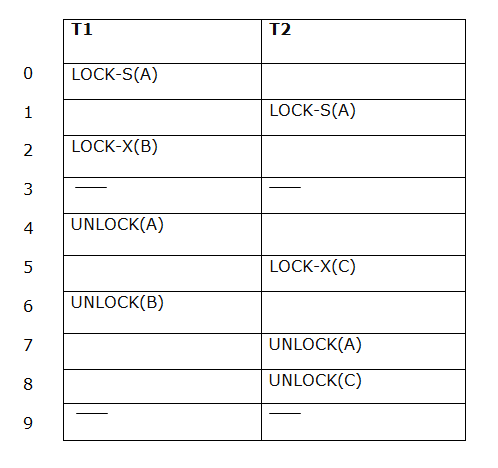
The following way shows how unlocking and locking work with 2-PL. Transaction T1:
Transaction T2:
4. Strict Two-phase locking (Strict-2PL)
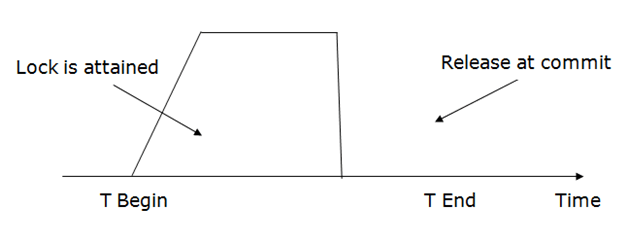
It does not have cascading abort as 2PL does.
Next TopicDBMS Time stamping Protocol
|
Related Links:
- DBMS Multivalued Dependency
- DBMS Inclusion Dependence
- DBMS SQL Set Operation
- Top 52 DBMS Interview Questions (2021)
- DBMS Transaction Processing Concept
- DBMS States of Transaction
- DBMS Schedule
- DBMS Conflict Serializable Schedule
- DBMS View Serializability
- DBMS Recoverability of Schedule
- DBMS Tutorial | Database Management System
- DBMS Failure Classification
- DBMS Concurrency Control
- DBMS Lock based Protocol
- DBMS Log-Based Recovery
- DBMS Checkpoint
- DBMS Timestamp Ordering Protocol
- DBMS Validation based Protocol
- DBMS Thomas Write Rule
- DBMS Multiple Granularity
- DBMS Sequential File Organization
- DBMS Recovery Concurrent Transaction
- DBMS Characteristics of SQL
- DBMS File organization
- DBMS Heap File Organization
- DBMS Hash File Organization
- DBMS B+ Tree
- DBMS RAID
- DBMS B+ File Organization
- DBMS Indexed Sequential Access Method
- DBMS Cluster File Organization
- DBMS Hashing
- DBMS Static Hashing
- DBMS Dynamic Hashing
- DBMS SQL Introduction
- DBMS Advantage of SQL
- SQL Commands: DDL, DML, DCL, TCL, DQL
- DBMS SQL Operator
- DBMS SQL Insert
- DBMS SQL Update
- DBMS SQl Datatype
- DBMS SQL Table
- DBMS SQL Select
- DBMS SQL Index
- DBMS SQL Sub Queries
- DBMS SQL Clauses
- DBMS Generalization
- DBMS Specialization
- DBMS vs Files System
- DBMS Architecture
- DBMS SQL Delete
- DBMS SQL View
- DBMS Three schema Architecture
- DBMS Data model schema and Instance
- DBMS Join Operation
- DBMS Notation for ER diagram
- DBMS Relational Calculus
- DBMS Data Independence
- DBMS Language
- DBMS ER model concept
- DBMS Mapping constraints
- DBMS Keys: Primary, Foreign, Candidate and Super Key
- DBMS Aggregation
- DBMS Join Dependency
- DBMS Convert ER into table
- DBMS Relationship of Higher Degree
- DBMS Relational Model concept
- DBMS Relational Algebra
- DBMS Integrity Constraints
- DBMS Functional Dependency
- DBMS Inference Rule
- DBMS Normalization: 1NF, 2NF, 3NF and BCNF with Examples
- DBMS Transaction Property
- DBMS Testing of Serializability
- DBMS 1NF
- DBMS 2NF
- DBMS SQL Aggregate function
- DBMS SQL Joins
- DBMS 3NF
- DBMS BCNF
- DBMS 4NF
- DBMS 5NF
- DBMS Relational Decomposition

